Robotic Process Automation (RPA) is rapidly gaining traction around the globe, and it is now regarded as an essential element of digital transformation actions. Over 78% of those who have already implemented RPA expect to significantly increase their investment in RPA over the next three years.
Like any program within a network, there’s always the risk of an attack, especially if key security principles were not considered during its implementation. Designing an RPA solution poorly can cause a serious breach of security controls and result in sensitive data being revealed to untrusted parties.
Besides, automating a process within an organization does not translate to you adequately securing the process. So, if you consider implementing RPA as part of your digital transformation, we’ve put together the best security practices for your organization’s benefit. Remember that choosing the right RPA developer is one of the essential parts of implementing Robotic Process Automation for your business.
What is RPA?
Robotic Process Automation is the use of scripts and software algorithms to effectively and securely automate the repetitive and mundane tasks that human resources in a company would usually perform.
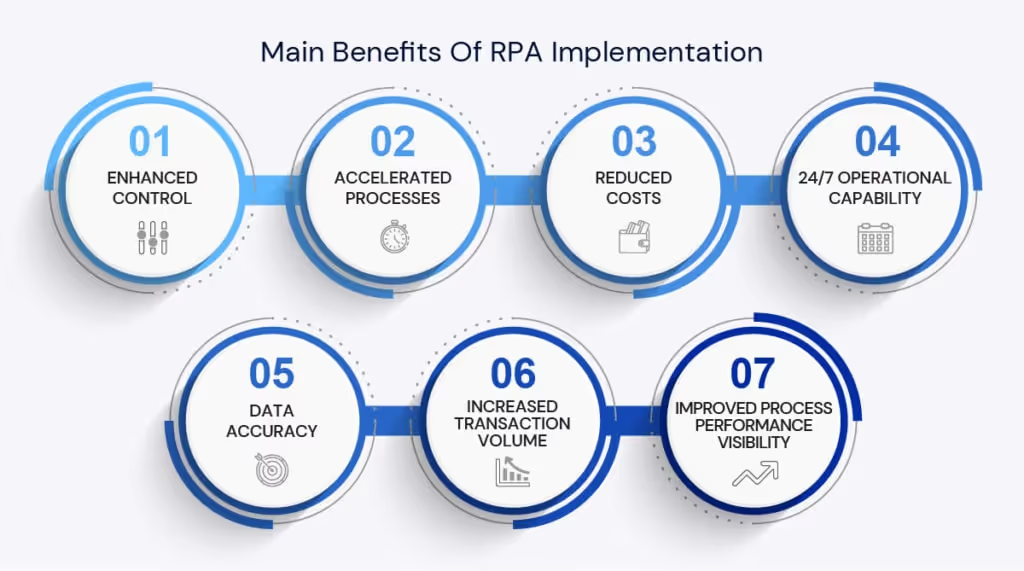
If applied and implemented in the right manner, RPA software algorithms can considerably improve productivity, accuracy, and quality of data and adherence. You can easily Implement RPA in finance and banking, real estate, or any other industry. Not just that, RPA is known to empower human resources to concentrate and focus on tasks that involve more human interaction and fulfilling work. Make sure that RPA is what you need on a call with our battle-proven RPA consultants.
Risks associated with RPA
One of the alluring features of RPA is its ease of implementation. As a result, many organizations’ departments and sectors can set up an RPA bot with IT or sometimes without letting IT know what they are up to.
While this seems like an advantage since most IT departments are stretched to the limit, it comes with many security risks. Many individuals or teams who implement RPA without partnering with a competent IT consultant most times have no idea about such security risks. Hence, the danger to the whole security system.
The primary risks associated with the integration of Robotic Process Automation can be viewed in two parts:
- Compliance risk
- Operational risk
1. Compliance Risks
Compliance risks stem from poor RPA governance, created by various implementation methods that bypass established software development lifecycles and ideal practices that meet data privacy, enterprise architecture, and network security.
2. Operational Risks
Operational risks include regulatory preparedness towards establishing barriers and everyday controls supporting business continuity and scalability.
The fundamental factor responsible for operational and compliance risk is the fragmented approach many organizations employ when establishing many of these automation programs.
To curb these risks, business and IT leaders must come together to choose the ideal RPA solution. Not just that, IT leaders must properly operate and design a Center of Excellence that can support a standard where IT tackles regulatory concerns, networks, and data.
On the other hand, business leaders need to concentrate more on identifying areas and best use cases of RPA within the organization. Therefore, RPA can effectively contribute to maintaining daily operations while developing programmers’ skills and implementing RPA bots.
Source of risks associated with RPA
It is important to have a vast understanding of Robotic Process Automation before integrating the software. And one of the comprehensive things to remember about RPA security is that many of the risks associated with RPA arise from poor care and lack of oversight.
Lack of proper planning and oversight of integrating RPA robots into an organizational system can cause more havoc than a strategic procedure. And for many IT leaders who don’t know, integrating RPA is not a solution to a firm’s lack of security hygiene. It is more likely to exacerbate security issues if they are not rectified first.
8 Best practices for Robotic Process Automation security
Proper security measures are crucial to implement Robotic Process Automation within an organization successfully. Sensitive data such as customer data and RPA credentials that the RPA software handles need to be protected as they can be exposed to attackers. Proper security frameworks and governance are important to mitigate these risks.
There are about eight security practices IT leaders and professionals can carry out to address these security failures and risks in RPA projects.
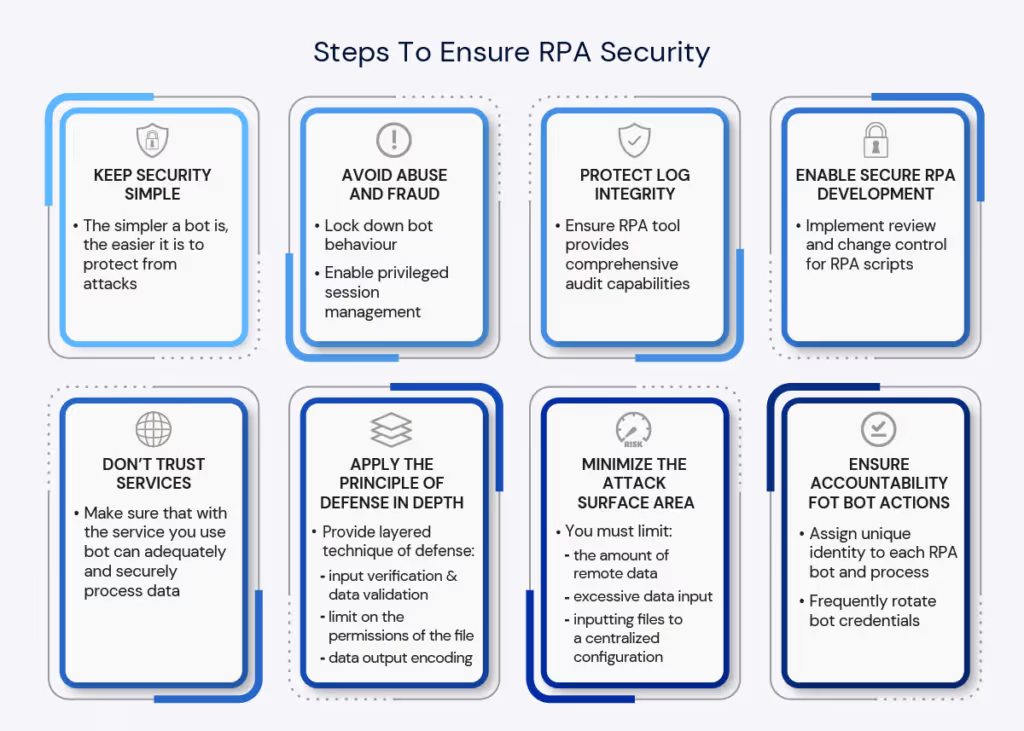
1. Ensure accountability for bot actions
Many firms and organizations during the Covid pandemic rushed to implement RPA software and algorithms. Most of these implementations were done to reduce the cost of performing repetitive and menial tasks while also reducing cost. However, most firms failed to differentiate between bot identities and bot operators. Hence no accountability was set for bot actions.
You must ensure accountability for bot actions to keep the RPA project security tight and secured. This is done by assigning a special identity to every RPA bot and process. Furthermore, implementing password and username authentication along with a two-factor human-to-system will also go a long way in securing your RPA project.
2. Minimize the attack surface area
Attackers look for the weakest avenue in a system to attack and exploit a security system hence the need to defend your avenues from all forms of attack. The fewer weak avenues of attack found in a security system, the harder it is to hack by attackers.
To ensure you have a reduced surface area attack, you must limit;
- the amount of remote data
- excessive data input
- the services and connections they both utilize
- inputting files and formats to a centralized, single, standard configuration.
Implementing these approaches will go far in minimizing attack surface area while reducing the RPA bot’s complexity.
3. Don’t trust services
One of the important features of the RPA bot is its ability to work with various services from a wide range of sources. While this is an advantage, it can also be a disadvantage, as not all these sources can be trusted to contain safe data.
Therefore, as an IT professional, you should not consider all services or process data they gather as containing safe data. By assuming that all service data or API is untrusted, you naturally establish extra data validation and security controls to ensure the bot can adequately and securely process data.
4. Apply the principle of least privilege
Applying the principle of least privilege entails programming your bot only to have access to the exact resources and files it requires to carry out its tasks. To adequately secure your RPA project, ensure all elevated permission actions and executive rights are only utilized when needed. Furthermore, any account your bot uses to connect to remote sources should be supplied with just the next trial permissions required by the bot to carry out its task.
By doing this, sensitive and crucial data are not exposed in a cyber-attack as the RPA bot can’t execute any action outside the permission.
5. Protect log integrity
In the case where RPA security fails, the IT and security team will need to look at and review your logs. Organizations and firms usually store RPA loggings to a different system to ensure its safety and vouch for its forensic integrity.
As an IT and security leader, you must ensure that the RPA tool offers a comprehensive system-generated log without any voids that might impede the investigation.
6. Ensure secure RPA development
RPA development is always a continuous process as it needs to evolve and develop to tackle various threats and vulnerabilities. However, to speed up the rate of development, firms usually suspend security considerations till RPA algorithms are prepared to run.
To ensure secure RPA development, you must create visionary conversations and standard measures between the line of business and security teams. This can be done by establishing a risk structure that assesses RPA implementation. Not just that, testing RPA scripts with a unique emphasis on business log vulnerabilities will also go a long way in securing RPA development.
7. Apply the principle of defense in depth
Adequate software security requires a layered technique called defense in depth. This implies establishing numerous strategies to protect and secure RPA projects against attacks. For a procedure such as inputting file assets, it might require numerous approaches such as;
- input verification and data validation
- limit on the permissions of the file and
- data output encoding
After these procedures, the data output is displayed on the screen or passed to any output console.
8. Keep security simple
The simpler a bot is, the easier it is to protect from attacks. Like reducing the surface area of attack, keeping your bot security management as simple as possible will enhance its entire defense.
Conclusion
The digital world has exposed all sectors to various kinds of cyber-attacks and hacks, so security must be treated as serious business. To this end, IT consultants and developers who are experts in RPA must be employed to secure and protect the project adequately.
Flobotics is one of the top IT consulting companies (with experienced UiPath developers) that can adequately implement RPA software within your organization and protect your RPA from all security risks. We are just one call or message away if you need the best experts on RPA technology to book your free RPA consulting session.









.png)




